Unlock the complete
Logicmojo experience for FREE
Sign Up Using
1 Million +
Strong Tech Community
500 +
Questions to Practice
50 +
Jobs Referrals
Sign Up Using
Strong Tech Community
Questions to Practice
Jobs Referrals

 Logicmojo - Updated Dec 15, 2023
Logicmojo - Updated Dec 15, 2023
The major responsibility of an operating system is to distribute resources and services, including memory, hardware, processors, and data. The operating system also has tools for managing these resources, including a file system, a traffic controller, a scheduler, a memory management module, and I/O programs. A piece of software called an operating system controls how computer hardware is allocated. To ensure the proper operation of the computer system and prevent user programmes from interfering with the system's proper operation, the hardware must be coordinated appropriately.
Example: We request or pass our orders to the Operating System in a similar manner to how a boss delivers directions to his employees. The primary objective of the operating system is to improve user convenience, and the secondary objective is to utilise resources as effectively as possible.
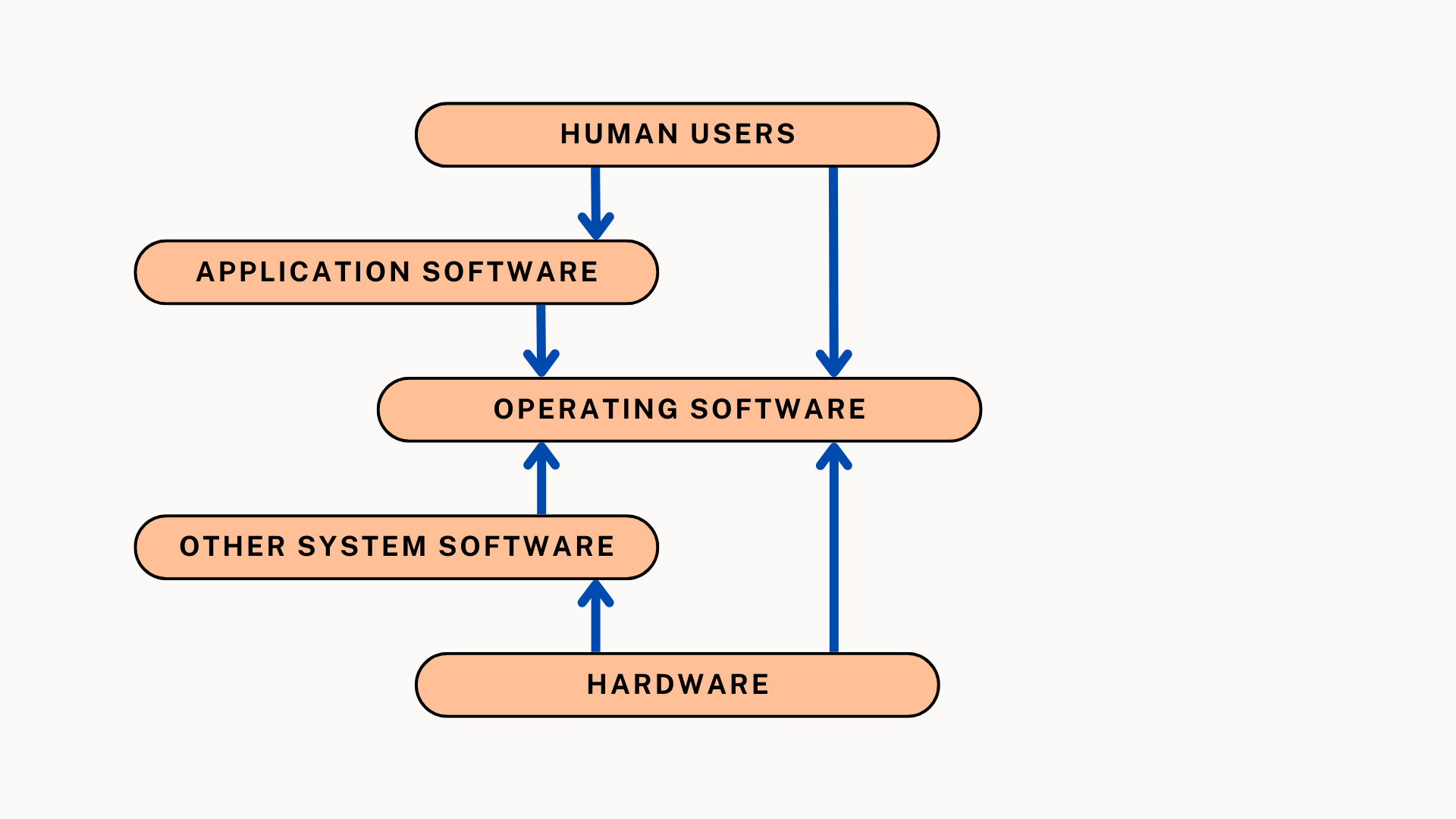
An operating system is a software on which application programs are executed and acts as a communication bridge (interface) between the user and the computer hardware.
An operating system is a piece of system software that serves as a gateway between the user and the hardware that powers a device. The gadget could be a phone, computer, or any other instrument. Along with serving as a conduit between you and the computer, it assists you with a variety of duties like computing, translation, etc. This is comparable to how your doctor functioned as the mediator between you and your disease, helping you to heal sooner. An operating system is created so that it can control all of a computer's processes and hardware resources. Windows and Linux are two popular operating system examples.
For a computer to run properly and support applications like Word, Excel, and even the Web, an operating system is a requirement. Your line of communication with the computer is the OS. It enables you to communicate with it and receive the desired responses in return. The Operating System produces all calculations.
The main task that the operating system performs is resource and service allocation, including the allocation of the following:-
🚀 Memory
🚀 Devices
🚀 Processors
🚀 Information
The operating system comes with programmes that can be used to manage these resources, including a traffic controller, a scheduler, memory management module, I/O programmes, and a file system.

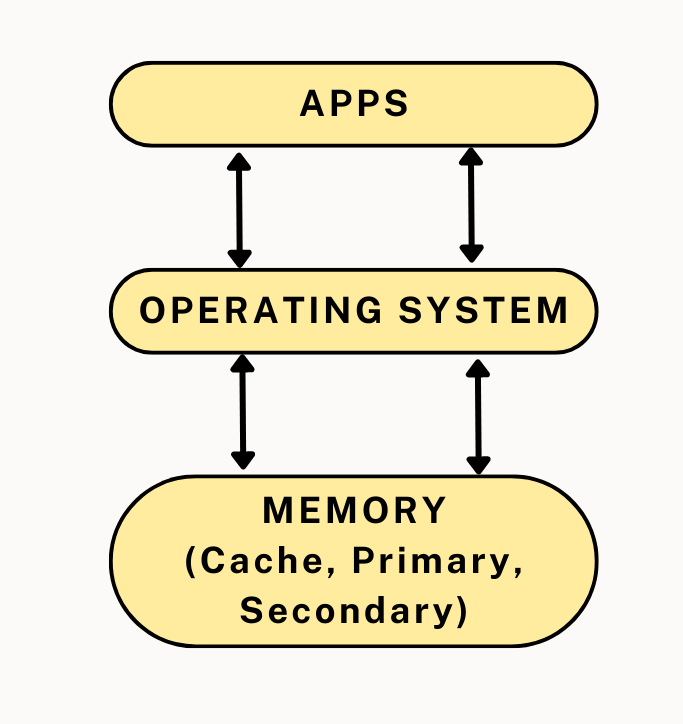
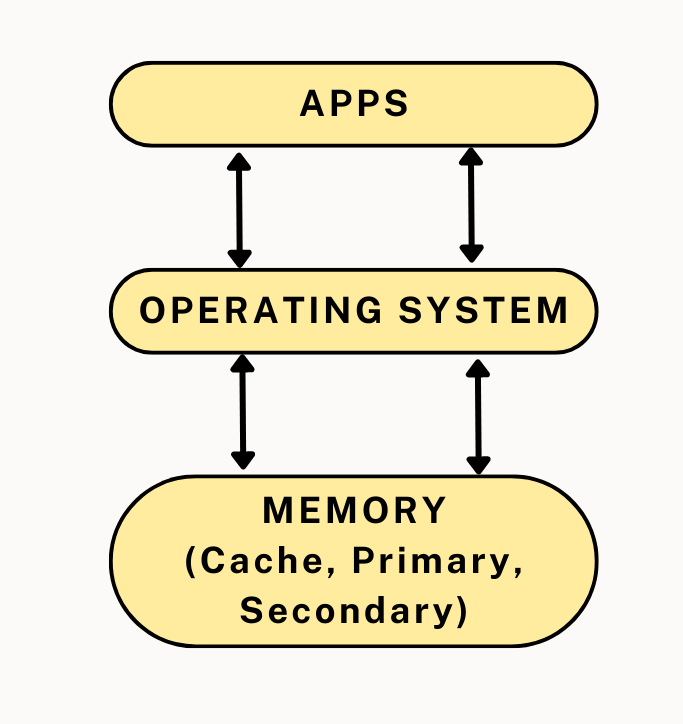
The Primary Memory or Main Memory is controlled by the operating system. Each byte or word in main memory has an address, and the array of bytes or words is quite big. The CPU may immediately access main memory, which is a quick form of storage. A programme must first be loaded in the main memory before it can be executed. The following tasks are carried out by an operating system to manage memory: It keeps track of the primary memory, or the number of bytes of memory that each user programme is using. the addresses of the memory that has already been assigned and the addresses of the memory that is still available. In multiprogramming, the OS determines the order and duration of memory access for each process. After a process requests memory, it allocates that memory to that process, and when that process has finished or is engaged in I/O activity, it deallocates that memory.
An Operating System aids you in achieving your goal of keeping your data secure in today's society. An operating system's capability increases its stability. An operating system makes use of firewalls to guard against and stop outside attacks. The system can only be used by people who have been given permission to do so.
Operating system keeps track of the amount of time and resources each job and user uses; this data can be used to monitor how much of each resource is being used by a specific user or group of users.
The OS controls the order in which processes access the processor and how much processing time each process receives in a multi-programming environment. Process scheduling is the name of this OS feature. The following tasks are handled by an operating system in terms of processor management.
🚀 monitors the state of the processes,
🚀 The programme that carries out this function is referred to as a traffic controller,
🚀 gives a process access to a CPU that is a processor
🚀 When a process is no longer necessary, the processor is de-allocated.
Device communication is controlled by an OS using the appropriate drivers. The operating system handles the following tasks for device management.
🚀 Keeping track of all the system's linked gadgets.
🚀 The input/output controller is a software that is designated by the operating system as being in charge of each device.
🚀 It determines which process has access to each device and how long it has that access.
🚀 When devices are no longer needed, it de-allocates them in an effective and efficient manner.
Files are where data is saved. We can create, edit, update, and delete files with the aid of an operating system. Additionally, it facilitates file transfers across devices. The physical entities that are stored on the hardware are seen as files.
Directories are used to structure a file system and make it easier to navigate and use. These directories might include additional directories and files. The following file management tasks are performed by an operating system. It keeps track of information storage locations, user access preferences, file status, and more. The file system refers to these resources in general.
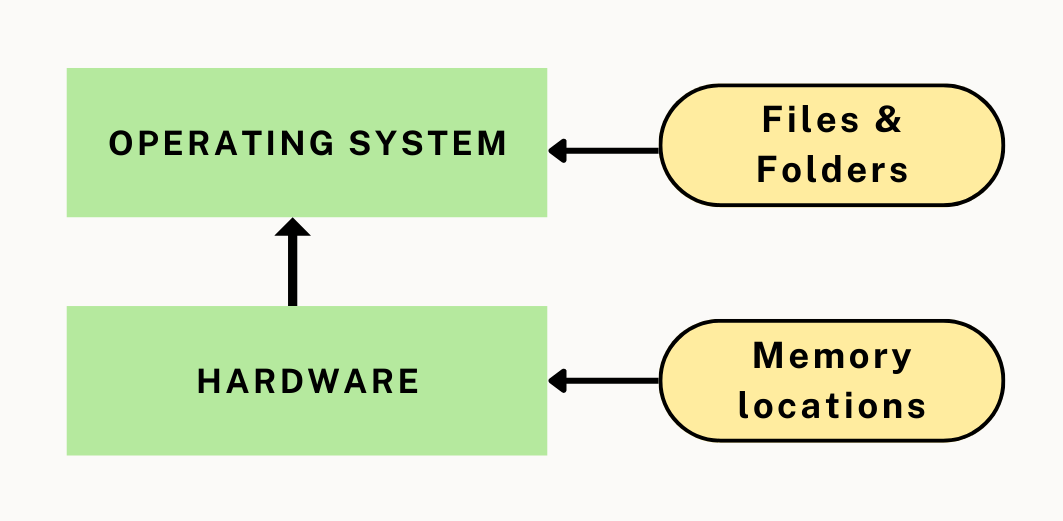
Between the user and the system hardware, the operating system acts as a bridge.
As needed by the user, it organises and allocates tasks to various components of the software, such as interpreters, compilers, etc.
The operating system must monitor the many simultaneous activities, defects made, and interruptions, if any. It may decide to terminate the programmes under consideration or immediately notify users of faults. By identifying which applications or processes have an impact on CPU and memory consumption and reduce it, system monitoring aids in our understanding of the system's state.
Monitors the condition of the entire system to enhance performance. For a thorough picture of the system health, records the time between service requests and system responses.
By giving crucial information required to solve problems, this can boost performance.
Additionally, it provides us with the data we need to diagnose system-related problems. The Task Manager screenshot that follows provides information on the CPU and Memory Utilization of several Windows Operating system activities.

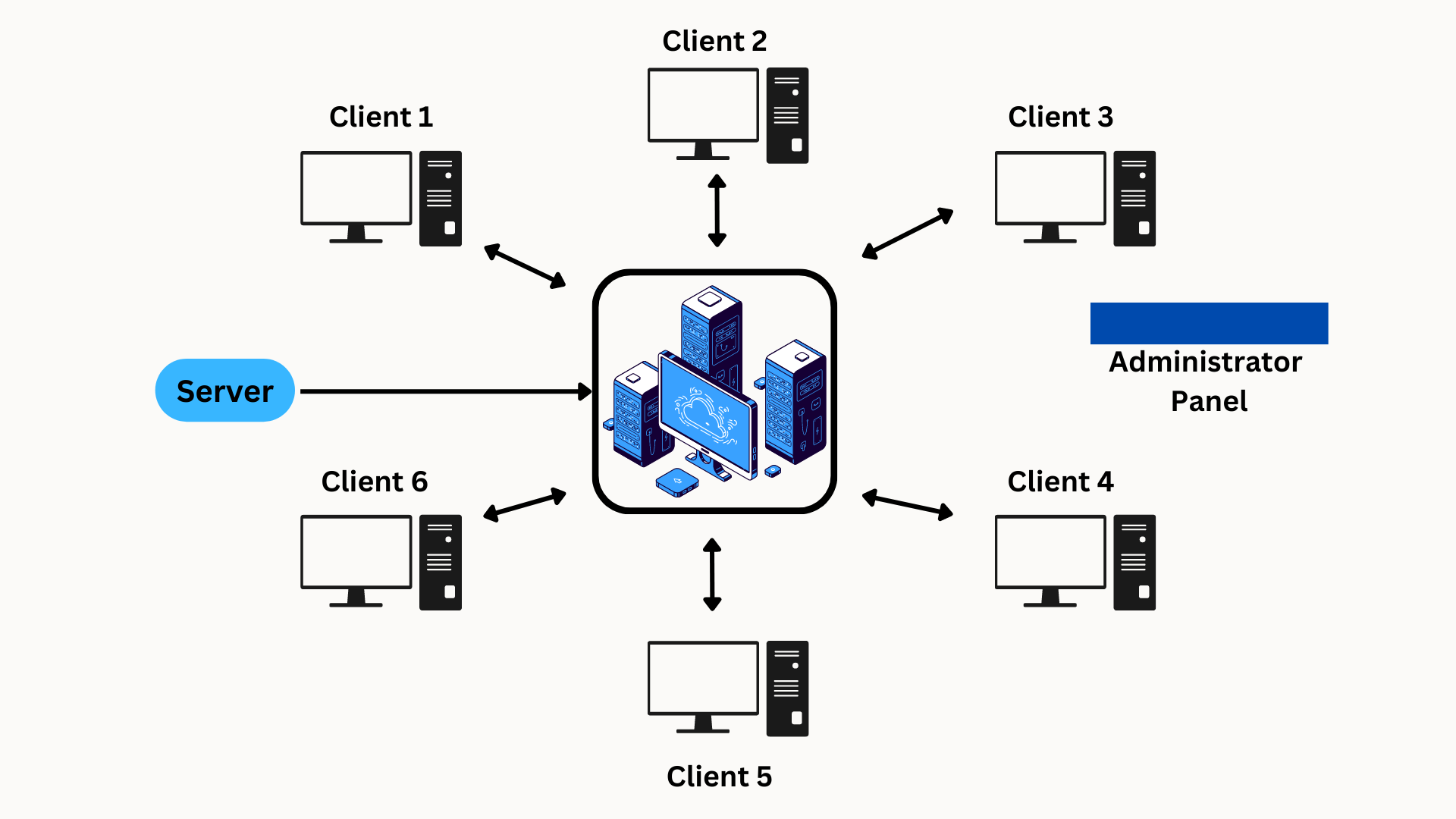
Networking highly depends on operating systems. Distributed systems are a typical example, where a server OS can guarantee consistency among the distributed PCs.
The operating system in such a system enables the connection of several independent and geographically dispersed computers via a single communication channel.
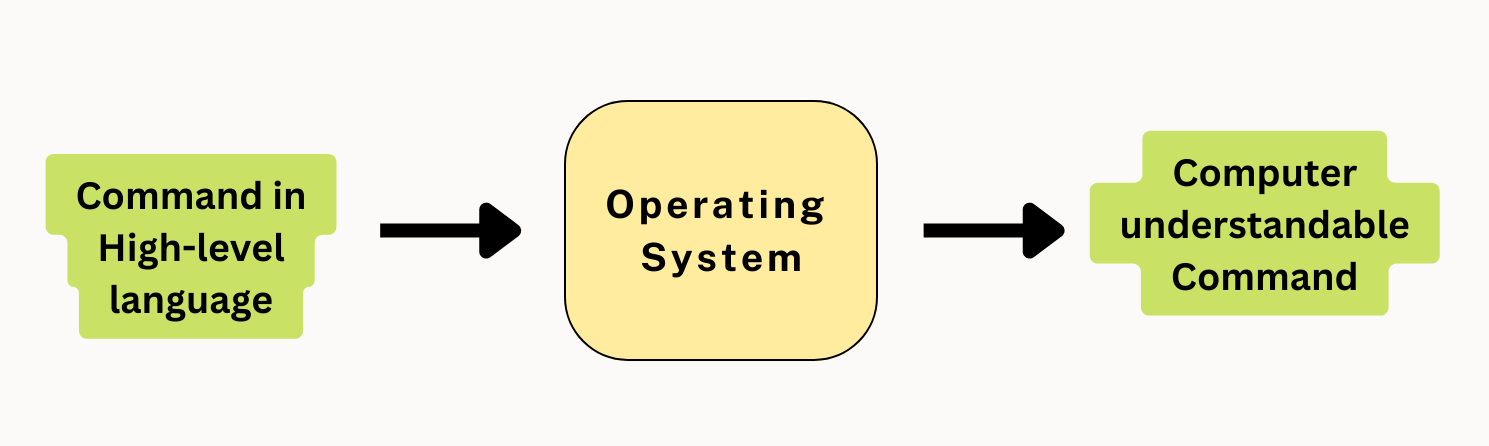
As a user, you enter commands in such a language that you understand. Because the computer primarily understands 0s and 1s (binary language), the operating system handles command interpretation and then directs the resources to process them.
Additionally, the operating system offers other services to the computer system.
The following list includes some of the services that the operating system offers to users:
A. Program Execution:
The Operating System is responsible of the execution of all programmes, whether they are user programmes or system programmes.
The Operating System employs diverse resources available for the efficient execution of all types of functionalities.
B. Manipulation of File System:
The Operating System is responsible for making decisions on the storage of all forms of data or files, i.e, floppy disk/hard disk/pen drive, etc.
The Operating System determines how data is manipulated and stored.
C. Error Detection and Handling:
The Operating System is in charge of detecting any form of error or bug that may arise during any task.
A well-secured operating system may also operate as a countermeasure to avoid any type of breach to the Computer System from any external source and possibly handle them.
D. Handling Input/Output Operations:
The Operating System is in charge of handling various types of inputs, such as those from the keyboard, mouse, and desktop. The operating system handles all interfaces for all types of Inputs and Outputs in the most appropriate way.
For example, the nature of all types of peripheral devices, such as mice or keyboards, differs, and the Operating System is responsible for processing data between them.
E. Resource Allocation:
By determining which resource will be utilised by whom for how long,
the operating system assures the proper use of all the resources that are accessible. The Operating System makes every decision.
F. Accounting:
The operating system keeps track of all the operations occurring simultaneously in the computer system.
The operating system keeps track of every detail, including the types of faults that were made.
G. Information and Resource Protection:
The Operating System has the responsibility of making the most secure use possible of all the data and resources on the machine.
Any attempt by an external resource to obstruct any kind of data or information must be rejected by the operating system.
The Operating System makes sure that all of these services are provided for users' convenience to make programming tasks simpler. The services offered by all different operating systems are essentially the same.
• An operating system is a user interface that facilitates interaction between a person and computer hardware.
• It is a crucial component of all computing equipment, including smartphones, laptops, cameras, and other gadgets. Some refrigerators and washing machines also feature them.
• The operating system controls files, processes, storage, external devices, and it also keeps an eye out for problems with the device.
• Additionally, it promotes security and shields the OS from obliteration.
• Additionally, it works to make sure that various tasks and processes are given the resources they need for a set period of time based on their respective priorities.
This concludes our discussion of "functions of Operating System". I hope that you gained knowledge about this amazing conncept and are now more interested to dive into the OS Function and features.
Good Luck & Happy Learning!!
A software program known as an operating system (OS) serves as a bridge between computer hardware and software programs. It is a crucial part of a computer system and is in charge of organizing and managing different hardware and software resources so that programs may run and user interactions can be facilitated.
An operating system's main responsibilities include:
1. Hardware Management: The operating system communicates with hardware elements such the CPU, RAM, storage devices, input/output (I/O) devices (such as the keyboard, mouse, and printer), and network interfaces. To ensure effective use of the hardware, it allots resources, schedules tasks, and controls memory.
2. Task and Process Management: The operating system manages and regulates how tasks or processes are carried out. It distributes CPU time to several processes, plans when they will execute, and organizes their interactions to make sure each program runs equally and effectively.
3. Memory Management: The operating system controls the computer's primary memory (RAM) and secondary storage (hard drives, solid-state drives), as well as other memory resources. In order to maximize memory consumption, it allots memory to processes, monitors the amount of memory that is accessible, and engages in memory swapping and paging.
4. File System Management: To arrange and manage files and directories, the operating system offers a hierarchical framework known as the file system. It manages the creation, deletion, and alteration of files and makes ensuring that data is accessed and stored securely.
5. Device management: The operating system handles and communicates with I/O devices, including keyboards, mouse, displays, printers, and network devices. It offers device drivers that make it easier for hardware and software applications to communicate, facilitating data transfer and managing device operations.
6. User Interface: To enable user interaction with the computer system, the operating system offers a user interface (UI). This can be done via a GUI or a command-line interface (CLI), which both offer visual components including windows, menus, icons, and buttons to streamline user interactions.
7. Security and Protection: The operating system makes sure that the computer system and its resources are secure and protected. To protect data and stop criminal or illegal activity, it maintains user access rights, offers authentication and authorisation systems, and enforces security regulations.
There are several sorts of operating systems, including Windows, macOS, Linux, and various mobile operating systems like Android and iOS. Each operating system is unique in terms of its target platforms, design philosophies, and functionality.
In conclusion, an operating system is an essential software element that controls the hardware resources of a computer, offers services to software programs, and streamlines user interactions. It is essential for ensuring that computer systems run effectively and securely.
1. Windows: Windows is Microsoft's most well-known operating system for personal computers (PCs). Around the world, it has been widely embraced by people and organizations. Windows has an intuitive graphical user interface, a sizable ecosystem of software programs, and broad hardware compatibility. Over the years, many Windows releases, including Windows 10, Windows 8, and Windows 7, have been made in response to various needs and technological breakthroughs.
2. macOS: The most widely used operating system for Apple computers, including Mac laptops and desktops, is macOS. It is produced by Apple Inc. and renowned for its user-friendly interface, seamless hardware integration, and sleek design. A large selection of productive and creative applications are available on macOS, which also boasts an effective and user-friendly interface. New features and improvements are added to the platform with each major release of macOS, including macOS Catalina, macOS Big Sur, and macOS Monterey.
3. Linux: Linux is a well-known open-source operating system that has become quite popular, especially in the worlds of servers, cloud computing, and embedded computers. The Unix operating system, on which Linux is based, is renowned for its reliability, security, and versatility. It provides a wide variety of distributions, each catered to certain user demands, including Ubuntu, Fedora, and Debian. Linux offers a wide range of customization possibilities, powerful command-line functionality, and a sizable library of free and open-source applications.
4. Android: Created by Google, Android is the most widely used smartphone operating system. The vast majority of smartphones, tablets, and other mobile devices worldwide run on it. The Google Play Store has a huge number of applications, and Android enables seamless interaction with Google services in addition to a user experience that is extremely configurable. A sizable developer community makes it possible to construct a wide range of cutting-edge mobile applications.
5. iOS: The iOS operating system was created exclusively for iPhones, iPads, and iPod Touches from Apple. It is renowned for its ease of use, security, and easy syncing with Apple's ecosystem. iOS offers an elegant user interface, efficient performance, and a carefully chosen collection of apps via the App Store. It provides seamless user experience within the Apple ecosystem thanks to its strong connection with other Apple products and services.
It's important to remember that the popularity of operating systems might change depending on the type of device, the location, and the individual user preferences. The aforementioned operating systems have become well-known because of their functions, user interfaces, and sizable user bases. Each operating system meets a different set of requirements and provides special benefits, which helps explain why they are so well-liked in their specialized fields.
The many operating systems based on task management are described in detail below:
1. Monotasking Operating Systems: Also referred to as single-tasking operating systems, monotasking operating systems are made to only run one program at a time. Until it is finished running or is terminated, these operating systems devote all of their computational resources to a single program. The operating system can then load and run the following program after the previous one has completed its execution.
Early computer systems, where resources were scarce and software required exclusive access to the hardware, were dominated by monotasking operating systems. Early iterations of MS-DOS (Microsoft Disk Operating System), for instance, are examples of monotasking operating systems.
2. Multitasking Operating Systems: As the name implies, multitasking operating systems have the capacity to run many programs simultaneously. By dividing up the available computing resources among them, they enable the simultaneous execution of numerous tasks or programs.
Operating systems that support many tasks provide effective resource management and increased user productivity. They offer methods for dividing up memory, CPU time, and other resources among various programs. The operating system rotates between running processes, allocating a certain amount of CPU time to each one.
There are two distinct methods for managing tasks in multitasking operating systems:
A. Preemptive Multitasking: In preemptive multitasking, the operating system has the power to forcibly switch from one program to another while it is still running. Tasks are scheduled by the operating system using predetermined priorities, time windows, or other factors. Even when the program's execution isn't complete, it can still interrupt it.
Preemptive multitasking makes ensuring that many programs are run fairly and quickly. It keeps a single program from controlling all system resources and enables the operating system to properly handle time-sensitive tasks. Preemptive multitasking is a technique used by several operating systems, such as Windows, macOS, and contemporary Linux.
B. Cooperative Multitasking: Each program in cooperative multitasking is in charge of voluntarily handing over control to the operating system after it has completed its present task. By sacrificing CPU time so that other programs can run, programs cooperate. A software may potentially monopolize system resources and have an adverse effect on system performance if it is unable to give up control.
Cooperative and well-behaved programs are necessary for cooperative multitasking. It depends on the programs to set their own schedules and guarantee equitable resource use. Cooperative multitasking is used by some embedded devices and earlier versions of Mac OS (before Mac OS X).
Various factors, including system constraints, performance considerations, and the desired amount of control over task execution, influence the decision between preemptive and cooperative multitasking.
The ability of operating systems to run many programs at once can be used to classify them as monotasking or multitasking. Operating systems that support multiple tasks further categorize them as cooperative multitasking, in which applications voluntarily cede control to the operating system, and preemptive multitasking, in which the operating system determines when to switch between programs. The system's needs for resource usage, responsiveness, and program behavior determine the selection of the best task management strategy.
There are many benefits to using an operating system, including:
1. Efficiency: By managing a computer system's resources, the operating system is essential in increasing a computer system's efficiency. It distributes and arranges the use of the CPU, memory, storage, and other resources among various tasks and programs. The operating system makes sure that these resources are used effectively by effectively controlling them, which enhances system performance and responsiveness.
2. Security: Operating systems offer security features to guard against hostile activity, unauthorized access, and data breaches. They incorporate functions like access control, user authentication, encryption, and firewall safety. To protect sensitive data and stop illegal access to system resources, the operating system handles user accounts, permissions, and limits.
Operating system providers often release security updates and patches to fix flaws and guarantee system security.3. Usability: Operating systems offer a user-friendly interface that makes it easier for people to engage with computers. They provide graphical user interfaces (GUIs) with simple visual components like windows, menus, icons, and buttons to make it simpler for users to navigate and complete tasks. Operating systems offer standardized practices and norms for user interactions, which lower the learning curve and improve usability. Additionally, they provide tools for system configuration, file management, and program launch, all of which help to make the experience streamlined and user-friendly.
4. Portability: By allowing them to be transferred from one machine to another, operating systems offer portability. This implies that software programs created for a specific operating system can function on a variety of hardware setups that support that operating system. Operating systems offer a layer of abstraction between hardware and software, enabling programmers to create applications that can operate on a range of hardware platforms without requiring major changes. The creation, distribution, and compatibility of software on many computer systems are all made easier by this portability.
Operating systems provide features including task management, device drivers, networking capabilities, file system administration, and assistance with software creation in addition to these advantages. These aspects help make computer systems more functional, effective, and usable as a whole.
Operating systems serve a significant role in enabling users to efficiently utilize computer systems and confidently carry out a variety of tasks by offering efficiency, security, ease of use, and mobility.
Based on a variety of elements and traits, there are numerous types of operating systems. Although it is difficult to classify operating systems into a clear set of kinds, the following six are widespread:
1. Real-time operating system (RTOS): RTOSs are created to manage time-sensitive applications where operations need to be done within predetermined time frames. They ensure prompt execution of activities by prioritizing them according to their urgency. Applications utilizing RTOSs include robotics, aeronautical systems, industrial control systems, and multimedia processing. Examples include VxWorks, FreeRTOS, and QNX.
2. Operating System for a Single User and a Single Task: This kind of operating system is made for a single user and a single task. It offers an easy-to-use user interface and frequently does not enable multitasking. This includes earlier iterations of operating systems like MS-DOS and Apple DOS.
3. Single-user, multi-tasking operating systems: These systems enable a single user to run a number of programs at once. These operating systems allow multiple programs to run simultaneously by allocating CPU time to them. Windows, macOS, and numerous Linux distributions are examples.
4. Multi-user Operating System: Multi-user operating systems enable several users to access the system and execute separate programs at the same time. To ensure fair utilization and security, these systems control user accounts, permissions, and resource distribution. Multi-user operating systems include UNIX, Linux distributions, and server editions of Windows, for instance.
5. Network Operating System (NOS): Network operating systems provide networked settings in which numerous computers are linked together and share resources. Tasks like file sharing, printer sharing, and network management are made easier by NOS. Examples include Novell NetWare, Windows Server, and Linux distributions set up as servers.
6. Distributed Operating System: A network of computers can be managed by a distributed operating system, which treats the network as a single, cohesive system. They make resource sharing and distributed component cooperation transparent. Large-scale systems like cloud computing and grid computing require distributed operating systems. Examples include Microsoft's Azure Sphere OS, IBM's AIX, and Google's Android.
It's crucial to understand that these divisions are not mutually exclusive, and various operating systems may fit into more than one category depending on their features and design philosophies. Additionally, as technology develops and fresh computing paradigms are introduced, new operating system kinds could appear.
There are a few drawbacks to using an operating system, including:
1. Price: One disadvantage of utilizing an operating system is that some operating systems, especially proprietary ones, can be pricey. Commercial operating systems frequently have a cost associated with them; users may need to buy licenses or pay subscription fees. For people or organizations with tight budgets, this cost may be prohibitive, especially when many licenses are required for numerous devices.
2. Complexity: Using operating systems can be challenging, particularly for users who are unfamiliar with their features and functionalities. It can occasionally be difficult for users to navigate and make good use of an operating system due to the quantity of options, settings, and configurations available. It may take some time and effort to become familiar with an operating system and tailor it to fit individual needs and preferences.
3. Safety: Operating systems may be subject to security intrusions. Operating systems have come under attack from hackers and other bad actors as they have become increasingly networked and accessible. Unauthorized access, data breaches, malware infections, and other security issues can result from operating system security flaws. In order to reduce these risks, it is essential to maintain operating systems up to date with the most recent security updates and adhere to recommended practices for system security.
4. Updates: To correct problems, improve speed, and address security concerns, operating systems require regular updates. Updates are important to maintain the system's stability and security, but because of the potential annoyance they pose, they are occasionally viewed negatively. Updates may need system restarts, halt ongoing operations, or cause compatibility problems with specific software programs. To guarantee a secure and dependable computing environment, it is crucial to keep the operating system updated.
It's crucial to remember that the disadvantages listed above are not necessarily present in all operating systems, and that their effects might change based on the particular operating system, the needs of the user, and the usage scenario. Operating systems are crucial elements of contemporary computing systems since they frequently outweigh these limitations in terms of their advantages and functionality.
Ten typical operating system functions are listed below, each with a thorough explanation:
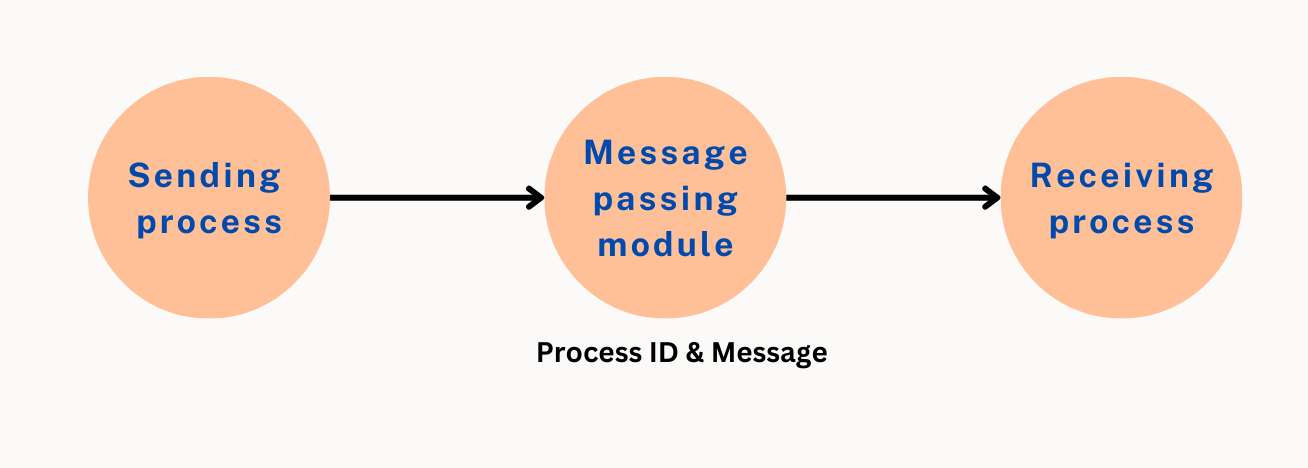
1. Process management: Processes, which are instances of programs being executed, are managed by the operating system. It establishes, schedules, and terminates processes, allots CPU time to them, and offers tools for synchronization and interprocess communication.
2. Memory Management: Memory management, which involves allocating and releasing memory to processes, is handled by the operating system. It effectively maintains memory resources, responds to memory allocation requests, executes memory swapping or paging as appropriate, and makes sure that processes are protected and isolated from one another.
3. File System Management: The file system management feature of the operating system allows for the addition, removal, and alteration of files and directories. It manages file access and permissions, handles data organization on storage media, and carries out file system integrity and security.
4. Device Management: The operating system controls the resources of devices such as network interfaces, hard disks, solid-state drives, and input/output (I/O) devices like keyboards, mouse, and printers. It manages resource sharing, device allocation, and device drivers, enabling processes to communicate with hardware.
5. User Interface: To enable user interaction with the computer system, the operating system offers a user interface (UI). It can be a graphical user interface (GUI), which provides visual components such windows, menus, icons, and buttons for user interactions, or a command-line interface (CLI), where users type text instructions.
6. Security and Protection: The operating system makes sure that the computer system and its resources are secure and protected. To stop unwanted access, it controls user authentication , access control, and permissions. To protect itself from threats and attacks, it employs security measures including encryption, firewalls, and antivirus software.
7. File and Data Backup: To safeguard data against loss or destruction, the operating system provides backup and recovery techniques. It offers utilities and tools for disaster recovery, data backup, and restoration, enabling users to create backups of crucial files and restore them in the event of data loss.
8. Networking and Communication: The operating system makes it easier for computers and other devices to network and communicate with one another. It offers networking protocols, manages network setups, provides network services, and allows processes to connect through networks, enabling resource sharing and teamwork.
9. Error Handling and Logging: While the system is running, errors are detected and dealt with by the operating system. It offers means for addressing errors, keeps track of system activities, and creates error messages or alerts to inform users or administrators of problems with the system. Problem-solving and diagnosis are aided by error management and logging.
10. System Monitoring and Performance: The operating system keeps an eye on system health, resource usage, and performance. In order to evaluate system performance, pinpoint bottlenecks, and improve resource allocation, it gathers statistics on CPU, memory, disk activity, and network traffic.
Together, these activities guarantee the secure and effective operation of a computer system. However, it's crucial to keep in mind that an operating system's precise features and functions can change depending on its kind (such as real-time, multi-user, or mobile) and intended use cases.
a description of the elements to take into account when selecting an operating system:
1. Your needs :
When selecting an operating system, take into account your unique wants and requirements. Choose the function for which you'll use the system. Examples of appropriate operating systems are Windows, macOS, and Linux distributions if you need one for general personal computing needs. You may need to look into specialised operating systems made for such uses if you need an operating system for specialized activities like server management, real-time processing, or embedded systems.
2. Your budget:
When selecting an operating system, take your budget into account. Some operating systems, especially those that are proprietary like Windows or macOS, could come with extra expenditures like license fees or subscription fees. Determine how much you are willing to pay on an operating system by assessing your financial resources. Open-source operating systems, such as Linux distributions, might offer affordable alternatives because they are frequently provided for free and have strong community support.
3. Your knowledge:
Take into account your level of knowledge and comfort with operating systems. It may be advantageous to continue with an operating system if you have expertise with it because you are already familiar with its user interface, capabilities, and environment. However, if you're willing to learn a new system or evaluate your options, you might want to think about using an operating system that matches your interests and offers room for improvement.
4. Your hardware:
Verify your hardware's compatibility with the operating system you're thinking of using. Specific hardware specifications for each operating system vary, including those for CPU architecture, memory, storage, and graphics capability. Make that your hardware satisfies or surpasses the minimal specifications stated by the operating system vendor. Also take into account whether the selected operating system has device drivers and software support for your hardware platform.
Software compatibility, the availability of tools and programs tailored to your needs, user interface choices, security features, and community support are possible additional considerations.
To make an informed choice, it's critical to investigate and compare various operating systems based on these criteria. Before making a decision, you might also think about testing or trying out various operating systems using live bootable discs or virtual machine settings. You can choose an operating system that best meets your demands and improves your computing experience by taking into account your requirements, budget, experience, and hardware.
Typically, the term "7 operating system" refers to Windows 7, a popular operating system created by Microsoft. The forerunner of Windows 8 and the replacement for Windows Vista, Windows 7 was made available on October 22, 2009.
While maintaining compatibility and user comfort, Windows 7 was created with the intention of fixing the flaws of its predecessor. Here are some of Windows 7's salient characteristics and specifics:
1. User Interface: When compared to Windows Vista, Windows 7's user interface has seen a number of improvements. The "Superbar," a more sophisticated taskbar that was included, with features including program pinning, thumbnail previews, and jump lists for rapid access to frequently used operations. Additionally, the Start menu was updated to give consumers a more streamlined and simple interface.
2. Performance and Stability: Windows 7 sought to offer enhanced system performance and stability over Windows Vista. It brought improvements and optimizations to memory utilization, resource management, and power efficiency. These enhancements led to quicker application launches, quicker boot times, and overall smoother operation.
3. Compatibility: Backward compatibility was a top priority for Microsoft while developing Windows 7, guaranteeing that hardware and software created for earlier iterations of the operating system would function properly on the current one. To handle older apps and devices, Windows 7 featured compatibility modes and virtualization technologies.
4. Networking and Connectivity: Windows 7 introduced enhanced networking features that made it simpler to connect to networks and control wireless connections. It introduced the HomeGroup feature, which made it simple for PCs connected to a home network to share files, printers, and media. Windows 7 also provided support for newer wireless technologies and improved Bluetooth functionality.
5. Security: To protect users and their data, Windows 7 added a number of security features. It featured the Windows Action Center, which offered a consolidated area for controlling security preferences, firewall settings, and system maintenance operations. Additionally, User Account Control (UAC) enhancements were included to Windows 7 to make it more configurable and unobtrusive while still ensuring system security.
6. Multimedia and entertainment: Windows 7 added enhancements to its multimedia and entertainment features. It debuted the Windows Media Center, a program for organizing and enjoying multimedia files including music, films, and pictures. Additionally, Windows 7 includes DirectX 11 for improved gaming experiences and included native support for a number of media types.
7. Editions: To meet the needs and requirements of various users, Windows 7 was made available in a number of editions. Windows 7 Starter (which offers little capability for netbooks), Windows 7 Home Basic, Windows 7 Home Premium, Windows 7 Professional, Windows 7 Enterprise, and Windows 7 Ultimate (which offers a wide range of functions for both home and corporate use) were among the editions offered.
For many years, Windows 7 was a widely used operating system and enjoyed great user appeal. It is crucial to remember that Microsoft stopped extended support for Windows 7 on January 14, 2020, and mainstream support for the operating system ended on January 13, 2015, respectively. For continued security upgrades and compatibility with emerging technologies, it is advised to think about utilizing a supported operating system like Windows 10.
Windows 11 is the latest major release of Microsoft's Windows NT operating system, released on October 5, 2021. It is a free upgrade to its predecessor, Windows 10 (2015), and is available for any Windows 10 devices that meet the new Windows 11 system requirements.
Windows 11 introduces a number of new features and changes, including:
⮞ A new Start menu that is centered on the taskbar
⮞ A new design language called Fluent Design
⮞ Support for Android apps through the Amazon Appstore
⮞ Improved gaming performance
⮞ Increased security features
Windows 11 is available in 110 languages and is designed for personal computing. It is a closed-source operating system, but some components are open source.
Here are some of the key features of Windows 11:
⮞ A new Start menu:The Start menu in Windows 11 is centered on the taskbar and has a new design. It includes pinned apps, recently used apps, and a search bar.
⮞ A new design language:Windows 11 uses a new design language called Fluent Design. This design language is based on the idea of motion and light, and it is used throughout the operating system, including in the Start menu, taskbar, and other UI elements.
⮞ Support for Android apps:Windows 11 supports Android apps through the Amazon Appstore. This means that you can now run Android apps on your Windows PC, just like you can on your Android phone or tablet.
⮞ Improved gaming performance:Windows 11 includes a number of new features that are designed to improve gaming performance. These features include DirectStorage, Auto HDR, and Variable Refresh Rate.
⮞ Increased security features:Windows 11 includes a number of new security features that are designed to protect your PC from malware and other threats. These features include a new security dashboard, a new sandbox for running untrusted apps, and improved encryption.
If you are currently using Windows 10, you can upgrade to Windows 11 for free. To do this, go to the Windows website and click on the "Download Windows 11" button. You will then be prompted to create a Microsoft account and sign in. Once you have signed in, you will be able to download and install Windows 11.
Windows 11 is a major upgrade over Windows 10, and it offers a number of new features and improvements. If you are looking for a new operating system for your PC, Windows 11 is a great option.
A deadlock in an operating system occurs when two or more processes are unable to move forward because they are each waiting for a resource that is being held by another process in the set. This circumstance results in a cyclic dependency that prevents any of the processes from moving further, resulting in a standstill. In concurrent systems, deadlocks are an undesired and difficult situation that can happen.
Let's examine the four prerequisites for a deadlock to happen, also known as the Coffman requirements, in order to comprehend deadlock:
1. Mutual Exclusion: Deadlock-related resources must be non-shareable, which means that only one process may access them at a time. When a process gets a resource, mutual exclusion makes sure that no other process can use it until it is relinquished.
2. Hold and Wait: In a deadlock situation, processes hold at least one resource while waiting for another resource that is being held by another process. This circumstance denotes a resource allocation deadlock caused by processes that do not surrender newly obtained resources before demanding further resources.
3. No Preemption: Processes cannot be preempted or have their resources forcefully taken away. A resource can only be voluntarily released by the process that is holding it. An interruption or resource reallocation to another process is prevented by this condition.
4. Circular Wait: A circular chain of processes must exist, with each process in the chain waiting for a resource held by the process behind it in the chain. Deadlock results from this cyclic dependency because no process can move forward without obtaining the resource that another process is holding.
A deadlock can happen when all four of these conditions are met at once. Once a deadlock has been achieved, the processes involved may not be able to go forward again without outside assistance.
Operating systems use several strategies, such as the following, to handle and reduce deadlocks:
1. Deadlock Prevention: To avoid deadlocks, this strategy focuses on removing one or more of the Coffman conditions. For instance, employing protocols that limit the maximum number of resources a process can retain at once or guaranteeing that processes obtain all essential resources at once before execution.
2. Avoiding Deadlocks: To prevent potential deadlocks, deadlock avoidance employs algorithms and heuristics to dynamically distribute resources. It necessitates familiarity with current resource demands and potential upcoming resource requests. Safe resource allocations can be determined using methods like Banker's algorithm and resource allocation graphs.
3. Deadlock Detection and Recovery: Algorithms for deadlock detection periodically scan the system for deadlocks. The operating system can take action to break the impasse after it has been identified. To end the deadlock, one or more processes may be terminated or their activities may be reversed to a previous checkpoint.
4. Deadlock Ignorance: Due to the low likelihood of deadlocks or the expensive cost of providing deadlock prevention or detection techniques, some operating systems, especially those employed in embedded systems or real-time environments, choose to ignore deadlocks. When this occurs, system designers put their attention on making sure the system is very reliable, reducing the likelihood of deadlocks by rigorous system design and resource allocation techniques.
For concurrent systems to be reliable and stable, deadlocks must be managed effectively. Operating systems use a variety of strategies to avoid deadlocks, identify them, and break them, ensuring that the system keeps running and that processes don't freeze for an extended period of time.
Paging is a memory management strategy used in operating systems to handle the virtual memory addressing scheme. It enables the operating system to allot memory to processes in predetermined chunks known as pages, which are subsequently translated into equivalent chunks of physical memory known as frames. Paging allows for effective memory use and offers a method of converting virtual addresses to physical locations.
More information about paging is provided below:
1. Virtual Memory and Pages: Each process in a system that makes use of virtual memory has a unique virtual address space. Pages are fixed-size divisions of the virtual address space. Pages typically have the same size, such as 4 KB. These pages give the process a logical address space.
2. Physical Memory and Frames: The primary memory, or RAM, is partitioned into fixed-size blocks referred to as frames. A frame's size corresponds to the size of a page. The system's actual physical memory is represented by frames.
3. Page Table: Each process includes a page table that keeps track of the mapping between virtual pages and actual frames. The operating system maintains a data structure for each process called the page table. The virtual page numbers to corresponding physical frame numbers are mapped in it.
4. Address Translation: A virtual memory address is broken down into a virtual page number and an offset within the page when a process accesses it. The physical frame number for a virtual page can be found by using the virtual page number as an index into the page table. The offset on the page doesn't change.
5. Page Faults and Memory Access: The operating system uses a page replacement mechanism to release a frame by swapping out a page when a page is not currently existent in physical memory (a page fault). The desired page is then read from secondary storage (such a hard drive) and read into the main memory.
6. Memory Protection: Because each process has its own page table, paging offers memory protection. Information concerning page permissions, such as read-only, read-write, or execute permissions, is included in the page table entries. This increases system security by ensuring that processes are prevented from accessing or altering memory that is not part of their allotted pages.
Paging has a number of benefits for memory management.
1. Efficient Memory Usage: Paging allocates memory in fixed-size blocks, allowing for efficient memory usage. Processes can now be loaded into non-contiguous physical frames because there is no longer a need for contiguous memory allocation.
2. Simplified Memory Management: By offering a unified and reliable addressing method, paging facilitates memory management. It does away with the necessity for difficult memory fragmentation methods like relocation or compaction.
3. Virtual Memory and Swapping: The concept of virtual memory, which allows programs to use more memory than is physically accessible, is made possible via paging. Physical memory can be made available for other processes by the operating system switching out pages that aren't used as frequently for secondary storage. This makes it possible for processes that need more memory than is actually available to be run effectively.
4. Memory Protection: By isolating each process's address space, paging offers memory protection. Data privacy and unwanted access are ensured since each process runs in its own virtual address space.
In contemporary operating systems, paging is a basic technology that enables effective memory management, virtual memory support, and memory protection. It gives programs a stable and secure environment to run in while enabling processes to use memory efficiently.